Data Access Governance
Secure Data Access Governance Solutions for Databases and
Data Lakes
Cyral’s data access governance solutions provide centralized, secure access management and real-time monitoring for structured and semi-structured data that is found in SQL and NoSQL databases and data lakes.
Know who has access to what data, how data is classified and provide continuous monitoring for auditing.

Why is Data Access Governance Important?
According to Gartner
“Data Access Governance (DAG) solutions have now become critical as they provide data access assessment, management and real-time monitoring for the unstructured and semi-structured data”. The report further states that, “DAG solutions help to provide the right level of access for users/groups. DAG also helps customers migrate some of their data repositories from on-premises to the public cloud by classifying data and cleaning up permissions beforehand.”
Gartner®, “Hype Cycle for Data Security, 2021”, Brian Lowans, July 27, 2021.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Benefits of Robust
Data Security Governance
Streamline access to data
Prevent data compromise
Enable strong yet simple privacy controls
Protect customer data
Meet regulatory requirements

No user workflow changes. No data modeling overhead.
Deploy Cyral’s data governance tools in front of existing data sources, and prevent backdoor access to data
Fine-grained access controlled with your existing IdP.
Identify users behind shared service accounts, enabling policies by user identities and SSO groups
Enable multi-cloud data security governance.
Specify Cyral policies by data type and help maintain centralized data security governance and privacy across CSP environments
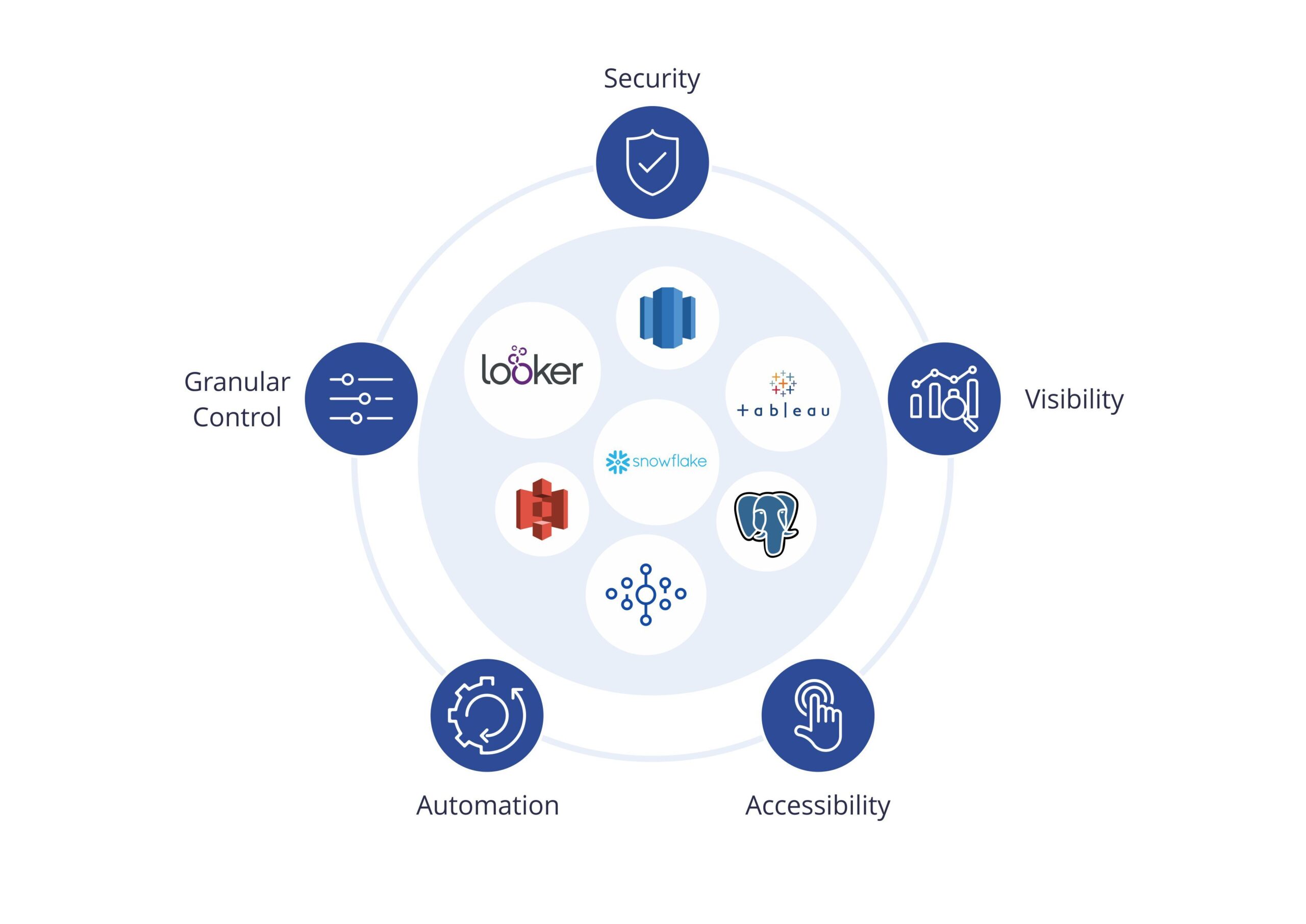
Spotlight Features

Simplify Secure Access Management for Cloud Data
Easily provision and manage access to cloud object storage, like S3, using your existing identity provider. Simplify user administration by mapping identities to IAM roles. Eliminate tedious role and credential specification from access workflows.
Easily Manage Access to your Data for Analytics and Modeling
Safely enable your data teams to access your data at scale. Eliminate the insecure use of shared service account credentials when accessing databases. Log every action to improve auditability and strengthen your overall data governance strategy.
Enriched Activity Logs for SIEM Integration
Collect identity-enriched logs and metrics for all activity against your databases, pipelines and data lakes. Get the real-time visibility and actionable context you need using your existing SIEM tools. Speed up troubleshooting and simplify audits improving confidence in your data governance framework.
Ready to Get Started?
Get started in minutes and explore how Cyral’s DAG solutions improve your data mesh governance and security. Read our Data Access Governance White Paper to learn more. You can also contact us to see a live demo.

