Data Governance
Easily Govern
Access to Data
Enterprises are investing in data governance to ensure the quality, security, and compliance of their data, which is essential for making better business decisions and driving growth. It forms the foundation for maintaining trust in data integrity and decisions based on that data.
Key Components of Data Governance
-
Define how data is collected, managed, accessed, and shared.
-
Ensure data security, compliance, integrity and protection.
-
Provide a framework for informed decision making.
-
Provides information about the structure, usage, and attributes of data.
-
Ensures that data is easily discovered, readily accessible, and effectively utilized.
-
Provides the meaning and context of data, enabling better decisions.
-
Maintains and improves the accuracy, consistency, and reliability of data.
-
Helps support quality standards, reduce errors and maintain trust in data.
-
Enables reliable reporting, better insights and confident decision-making.
-
Uphold adherence to regulations and standards to protect data.
-
Ensure data integrity, availability & confidentiality.
-
Reduce risk of breaches, foster trust and protect organization’s reputation.
-
Provides ongoing surveillance and assessment of data-related activities.
-
Ensures that data governance initiatives are effective and compliant.
-
Promotes a culture of accountability and transparency.
Data Governance, Access Control and Policy Automation Go Hand-in-Hand
Access Governance
Access permissions always aligned with risks and needs
Risk Mitigation
Detection and remediation happens as early as possible
Consistent Protection
Uniform policy application without lapses or oversight
Improved Agility
Reduces manual intervention and increases efficiency
Streamlined Audit
Continuous adherence to well-documented standards
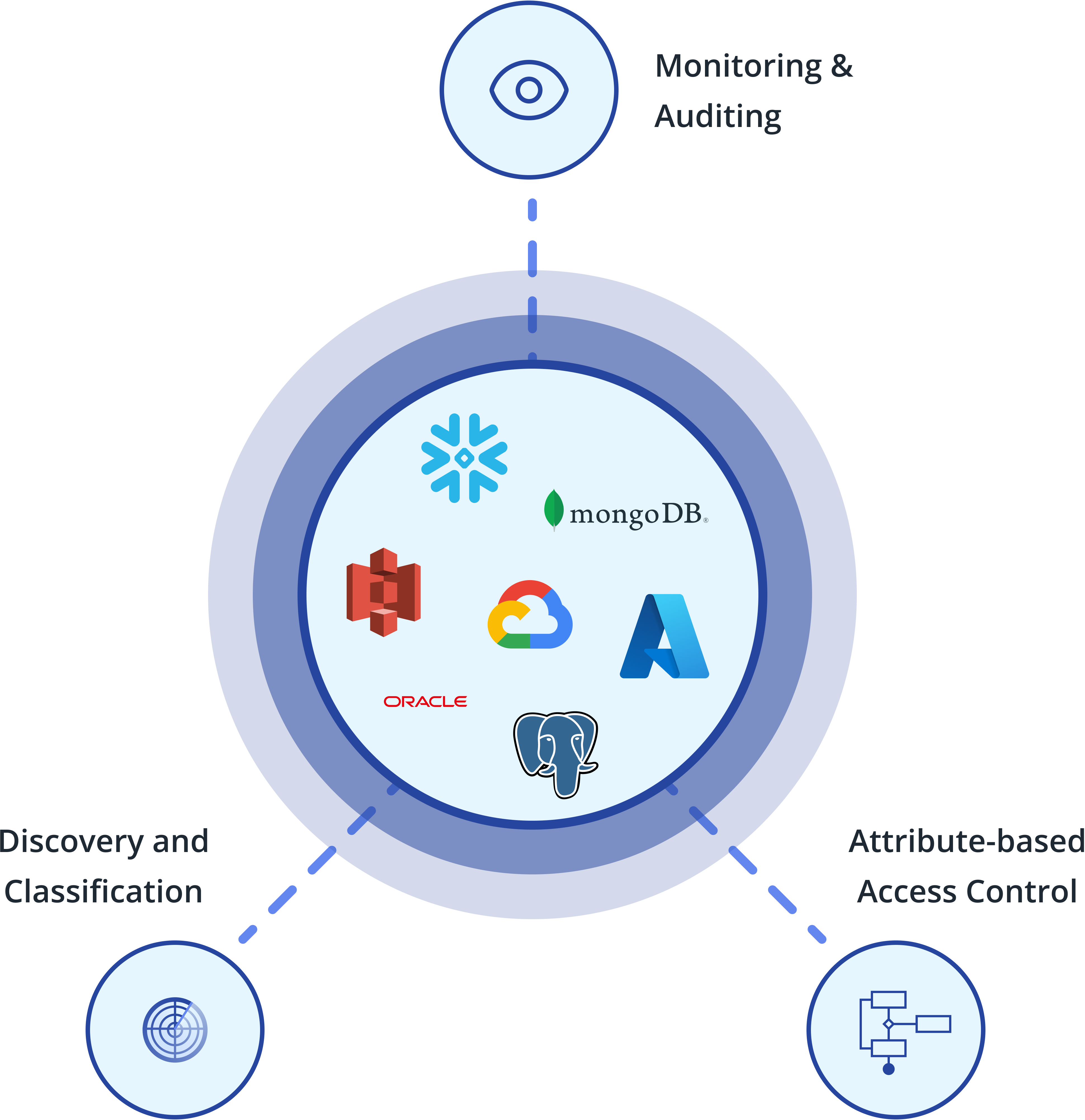
Cyral Brings Security to Data Governance
- Govern access to databases and data lakes in one place
- Ensure consistent and compliant control of access rights
- Improve user experience and simplify administration
- Eliminate the need to manage roles and permissions in database
- Implement and automate row-level and column-level security
- Simplify audits, governance and risk management
- Real-time visibility into all data activity by users and apps
- Centralized reporting of who can access what data
- Simplify compliance with regulations such as PCI, SOX, HIPAA, etc.
Ready to Get Started?
Get started in minutes and explore how Cyral’s modern data security platform can protect your data. You can also contact us to see a live demo.

