Trust at Cyral
We created Cyral to give organizations the power to secure their Data Mesh. As a company focused on data security, we are wholeheartedly committed to security of our own product and infrastructure, investing in compliance controls, respecting the privacy of our customers, and maintaining a stringent Code of Conduct, along with a responsible disclosure policy.
Security
Your security is of utmost importance to us at Cyral. We are committed to building our product and services on top of secure infrastructure, using best-in-class tools for security automation, and ensuring that strong controls are in place.

Cyral’s SaaS offering is hosted on AWS. AWS is the leading cloud provider, and we rely on their proven compliance tools to ensure we meet the requirements set forth in standards such as SOC 2. Cyral takes full advantage of a number of built-in AWS security and availability controls. We have designed our systems with high availability in mind and utilize a number of services to provide fault tolerance. Cyral also takes full advantage of IAM roles and best practices such as integrating our SSO provider and using Control Tower to manage AWS accounts.

Cyral encrypts all sensitive data, both at rest and in transit. The Cyral control plane currently supports TLSv1.2, with support for TLSv1.3 coming soon. The underlying services automatically use industry standard AES-256 encryption for storage. All communication between the Cyral sidecars and the Cyral control plane uses an RSA-based encryption tunnel. All communication between database clients and the sidecar, as well as traffic between the sidecar and the data repo, is fully encrypted in transit. For any internal encryption used in conjunction with a sidecar, the customer is responsible for managing the certificates. We continuously monitor our services to ensure that they are using industry standard best practices to secure data across the stack.
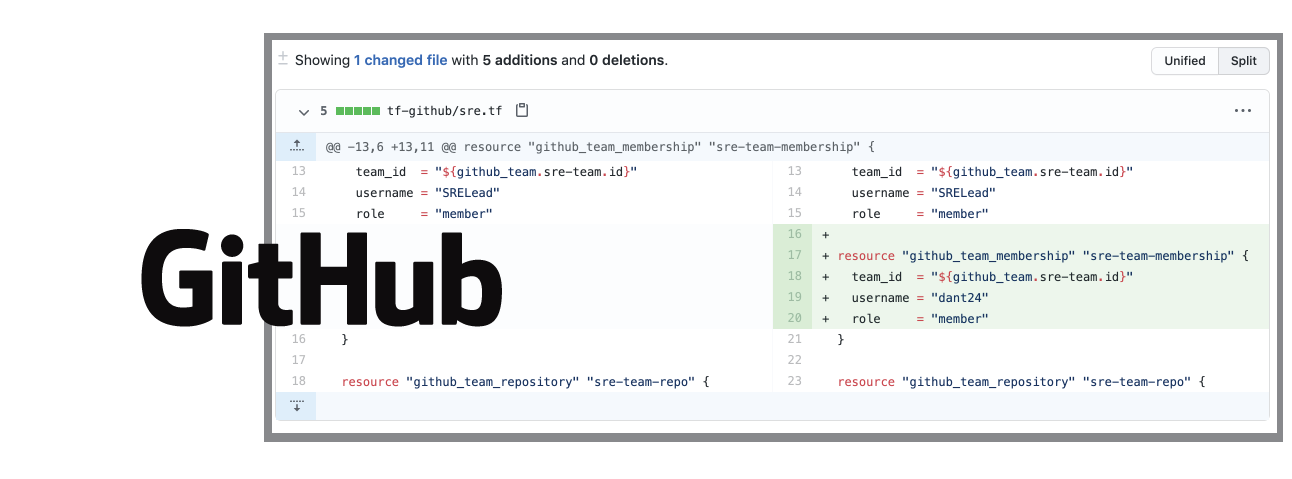
Cyral subscribes to a Security as Code methodology to continuously maintain and monitor our security posture from code development through to production deployment. We implement multiple security controls including source code review, vulnerability scanning of libraries, source code and infrastructure and continuous monitoring of all cloud providers and assets.

Cyral relies on G Suite for email, documents, and calendaring and we’ve implemented industry-standard practices including multi-factor authentication (MFA). We use MFA to protect all accounts on enterprise applications and third-party services such as AWS. Before we adopt any new service or vendor for internal use, we vet them for security using our security team’s documented approval process. Cyral maintains key IT policies and baseline standards to ensure that all IT devices and services meet our security standards at deployment time, and remain tracked and secure throughout their service life.

Cyral maintains active SOC 2 Type II compliance. Partnering with Vanta for ongoing automated security and compliance checks, along with undergoing regular audits by an independent firm, Cyral continues to meet the requirements of AICPA’s Trust Services Principles and Criteria. We take security seriously. To that end, the SOC 2 Type II report is validation of our commitment to adhering to security best practices and providing a level of assurance to our customers.
Privacy and Confidentiality
Our dedication to our customers’ privacy begins with our product architecture, ensuring that we minimize our interaction with and processing of our customers’ sensitive information. Internally, we have implemented security controls and procedures to ensure that customer data stays confidential and to ensure the integrity and availability of our product.

Cyral has developed an offering that consists of two portions: the sidecar and control plane. The sidecar is where the interception of data repository requests happens, and is deployed in our customers’ environments. The control plane is a cloud-based service which offers an operator’s view of what and where sidecars are deployed, and allows policies to be administered uniformly across all sidecars.
This design of our sidecar puts customers in complete control of their own data. All customer data, including data repository requests and responses, stays within their own environment.
To protect the privacy of your data, the Cyral sidecars send only essential information to the Cyral control plane. See “Minimizing information sent to the Cyral control plane,” below.

Cyral enforces a Code of Conduct for its staff and contractors. Upon joining our team, all team members must complete security training before they can begin to work on our products.

Cyral’s design minimizes our handling of your data. The Cyral sidecar service that protects your data repository send only non-sensitive information to the Cyral control plane; the contents of your repositories are never sent to Cyral or its control plane. For a list of the types of data the sidecar sends to the control plane, see cyral.com/docs/privacy.

We segregate access to data by role, with each role allowed only access to the data it needs. Role segregation is also enforced with respect our infrastructure and system design, with each design decision reviewed by a person outside the team responsible for the design.
Responsible Disclosure Policy
Data security is a top priority for Cyral, and Cyral believes that working with skilled security researchers can identify weaknesses in any technology. If you believe you’ve found a security vulnerability in Cyral’s service, please notify us; we will work with you to resolve the issue promptly. Thank you for helping to keep Cyral and our users safe!
Policy Guidelines
- If you believe you’ve discovered a vulnerability in our product or practices, please let us know by emailing us at security@cyral.com. Our team monitors this inbox and will respond within two days.
- We request that you provide us with a reasonable amount of time to resolve the issue before disclosing it to the public or a third party. We aim to resolve each critical issue within five business days of the day you report it to us.
- We request that you make a good-faith effort to avoid violating privacy, destroying data, or interrupting or degrading the Cyral service. Please only interact with accounts you own or for which you have explicit permission from the account holder.
Exclusions
While researching, we’d like you to refrain from:
- Any form of Denial of Service (DoS)
- Spamming
- Social engineering or phishing of Cyral employees or contractors
- Any attacks against Cyral’s physical property or data centers
- Issues in our blog (https://cyral.com/) and social media accounts (Facebook, Twitter, etc.)
- Issues in our support platform (https://support.cyral.com)
- Logout CSRF
- User existence / user enumeration
- Text-only injection in error pages
- Unconfirmed reports from automated vulnerability scanners
- Server and software versions in HTTP response headers
- Lack of password complexity restrictions
Future changes to this policy
We may revise these guidelines from time to time. The most current version of the guidelines will be available at https://cyral.com/trust.
Responsible disclosure by Cyral employees
Cyral’s own employees must also abide by this Responsible Disclosure Policy. Those who violate this policy may face disciplinary consequences in proportion to their violation. Cyral management will determine how serious an employee’s offense is and take the appropriate action.
What is Security As Code?
Security as Code is the methodology of codifying security and policy decisions and socializing them with other teams.
Secure Early and Often
In 1981, Barry Boehm published Software Engineering Economics, a look at the relative costs to fix an error at various stages of software development.
Contact Us
We’re always reachable
The Cyral security team welcomes feedback, questions, and suggestions. If you would like to talk to us, or report vulnerabilities found in our product or organization, please feel free to email us at security@cyral.com.

