On-Call Access Management
Simplify On-Call Access to Production Databases with Cyral and PagerDuty
Authenticate and authorize production database access for your on-call engineers. Improve team collaboration for reducing MTTR. Enforce least privileges and activity logging at every step.
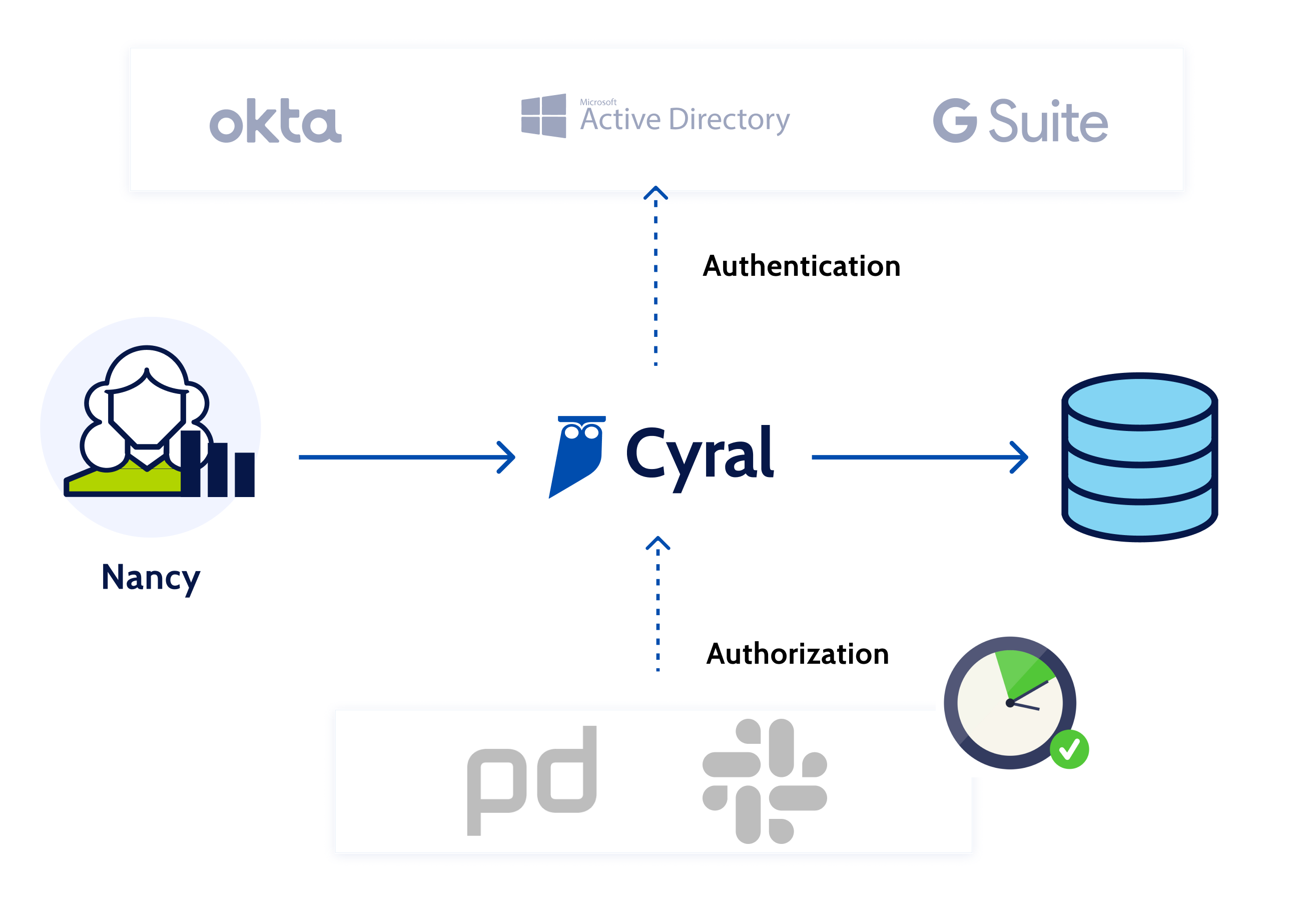
Centralized Authentication
Use your existing identity providers (like Okta, Active Directory or GSuite) to provision and manage access for your PagerDuty first responders so that they can get to work without delay.
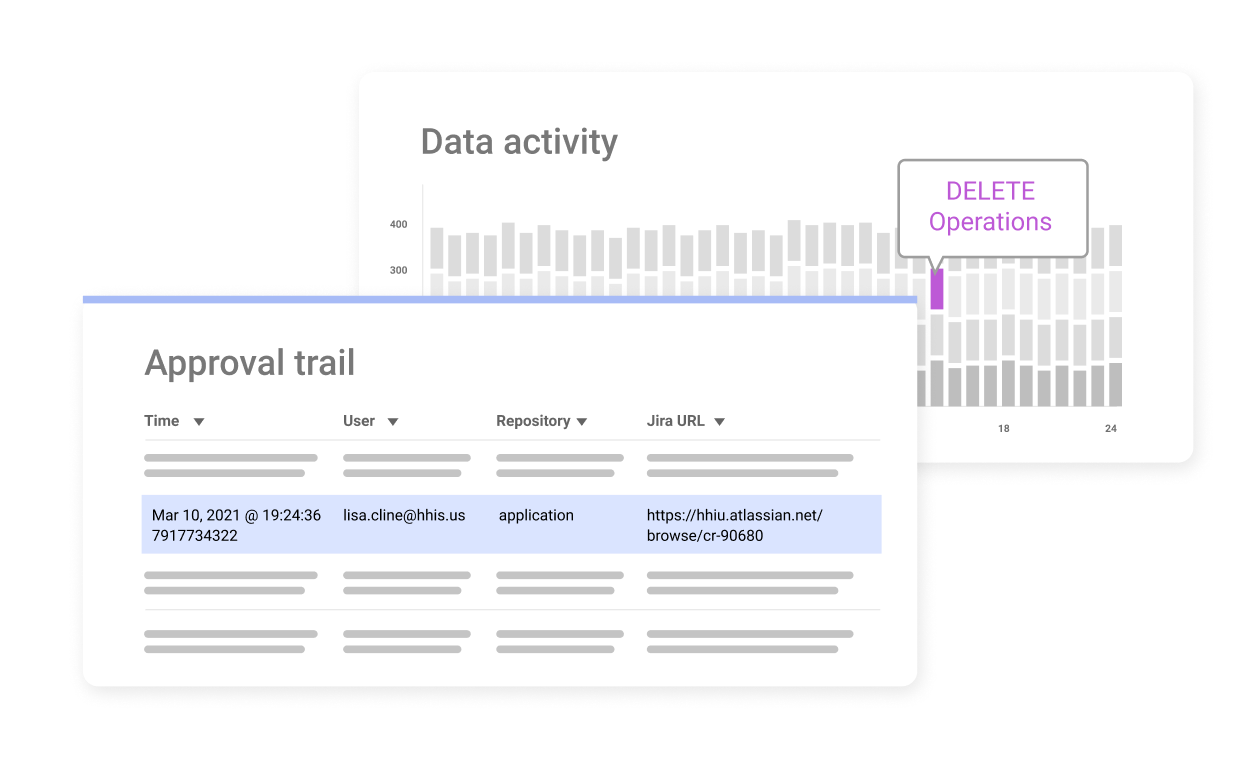
Audit Trail
Track a strong audit trail of all access approvals and durations. Gain detailed activity logs of what data was exposed and to who during the process.
Free Trial with PagerDuty
Sign up for our On-Call Access Management trial to experience how Cyral can provide you with a simple way to ensure that only authenticated on-call engineers are authorized to access specific production data resources during their on-call shifts.
Terminology
Terminology
On-Call Access Management
On-call access management, also known as incident access management, are the procedures and policies for providing necessary access to those employees who are on-call and or responding to an incident. Cyral makes it easy to authenticate and authorize production database access for on-call engineers and reduce mean time to recovery (MTTR). On-call engineers can tackle time-sensitive tasks while cloud infrastructure teams gain a simplified way to unblock investigations while limiting direct production data access.
Least Privilege Access
The principle of least privilege (PoLP), also known as the principle of minimal privilege or the principle of least authority, recommends that users, systems, and processes only have access to resources (networks, systems, and files) that are absolutely necessary to perform their assigned function. With Cyral you can automatically limit access to production data services to only on-call engineers to ensure they only have access to the required resources to get their jobs done. Let on-call engineers grant limited access to others for troubleshooting and guarantee only just-enough access to ensure no disruptive actions are taken.
Privileged Access Management
Privileged Access Management (PAM) refers to systems or services that can securely manage user accounts that have elevated permissions to critical systems, databases or resources. There are three types of privilege access management needs that most organizations use for on-call access management. Standing access, which most companies are trying to reduce because this poses security and compliance risk. Rotating access, as is the case with on-call, which most companies are trying to operationalize and automate because of the overhead. And on-demand access, also described as breakglass or P0, which most companies don’t have tooling for handling. Cyral operationalizes and automates all three types of access, limits activity based on customer-defined policies, creates audit artifacts, and captures rich activity logs complete with user identity.
Data Activity Monitoring
Database Activity Monitoring (DAM) refers to any solution that is used to actively monitor and analyze database activity. This technology is multipurpose, typically being used by organizations both to fulfill specific compliance criteria, as well as protect their most sensitive data from external hackers and malicious insiders. For on-call access management this is important for having strong audit trails. This can help with meeting compliance needs particularly for organizations holding customer billing data where PCI Requirement 7 mandates that those organizations “limit access to system components and cardholder data to only those individuals whose job requires such access.” It can also support SOC2 as it relates to (a) limiting the number of users that have access to production systems and customer data, (b) capturing elaborate audit information about activity in production data systems.

