Activity Monitor
Real-time Visibility
Get unified visibility into all data activity across all your data endpoints from any user, application, tool or service. Cyral helps organizations simplify audits, speed up forensics and reduce mean time to resolution.
Before

Before
Native reporting from data repositories is slow, lacks identity or context information, and makes troubleshooting and auditing complex. PII and other sensitive data is often exposed in them.
- Missing identity information and other context
- Heterogenous syntax and structure
- High performance and scalability penalty
After


After
Cyral transparently intercepts requests to all data endpoints, and captures activity in real-time. The logs, metrics and traces are enriched with identity and other context information.
- Enriched logs, metrics and traces
- Unified reporting syntax across all repositories
- Zero impact to performance and scalability
“Cyral is lightweight and runs in parallel with the data traffic, with no impact on performance.”

API-First Architecture
Easy to Set Up
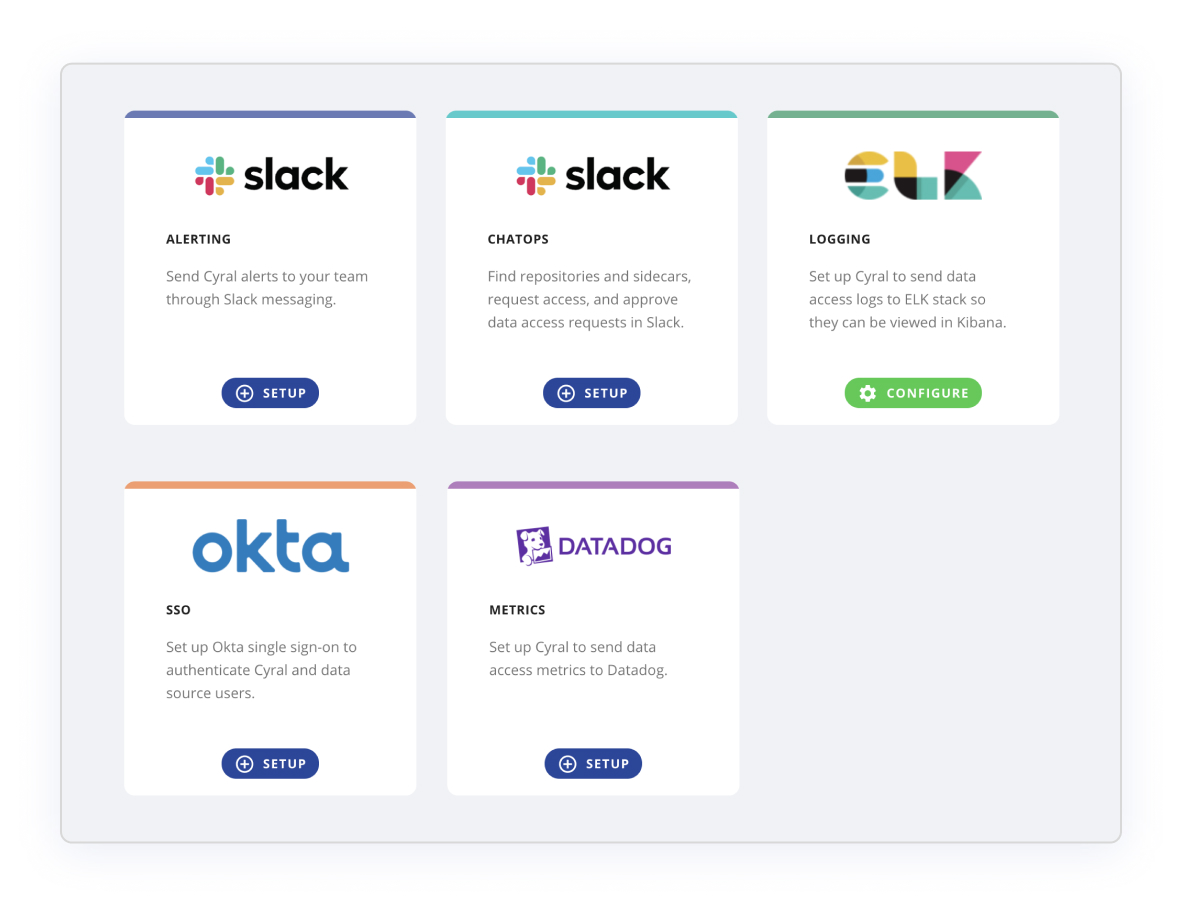

Integrate Cyral with your favorite reporting tools
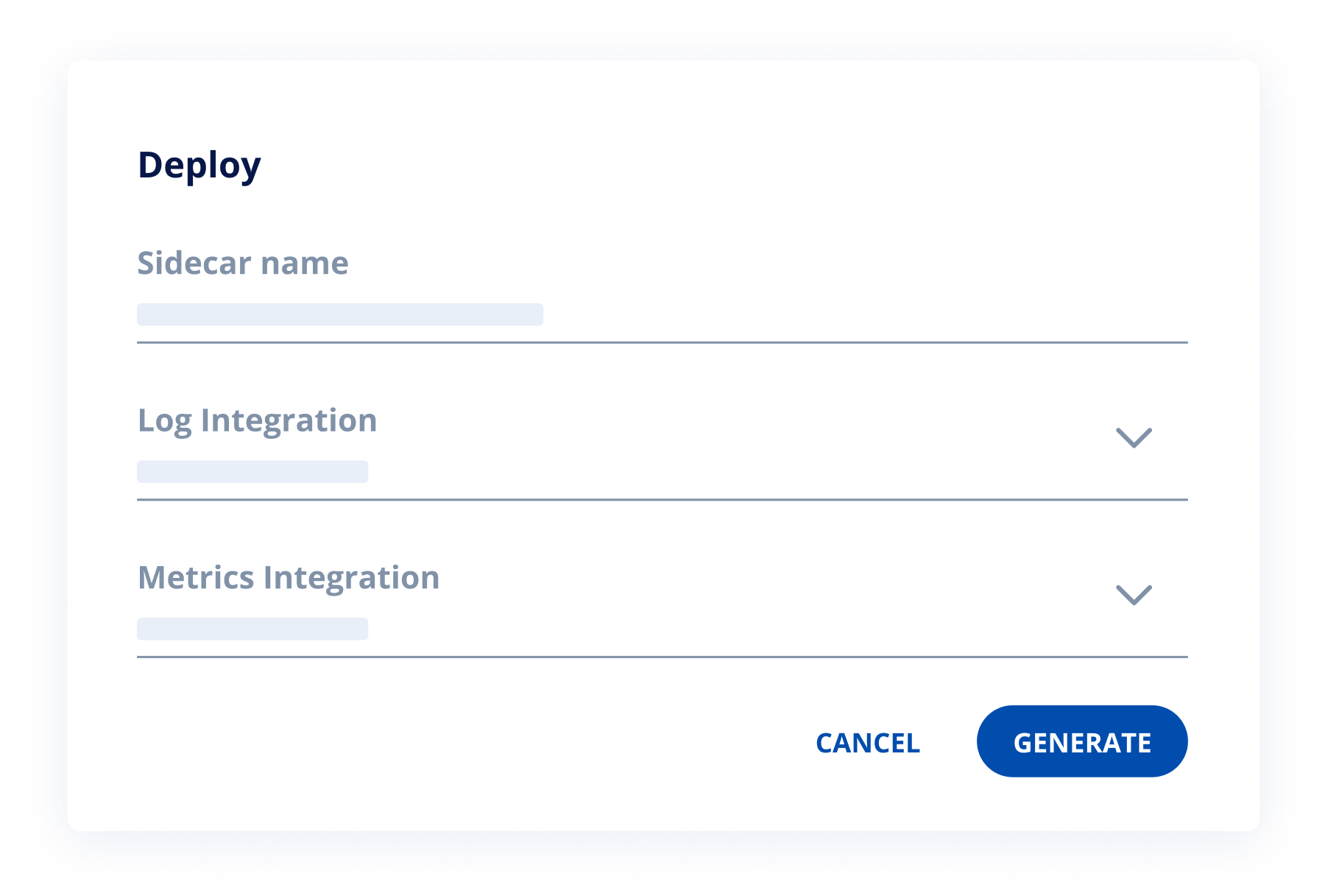

Specify which tool to use for each repository
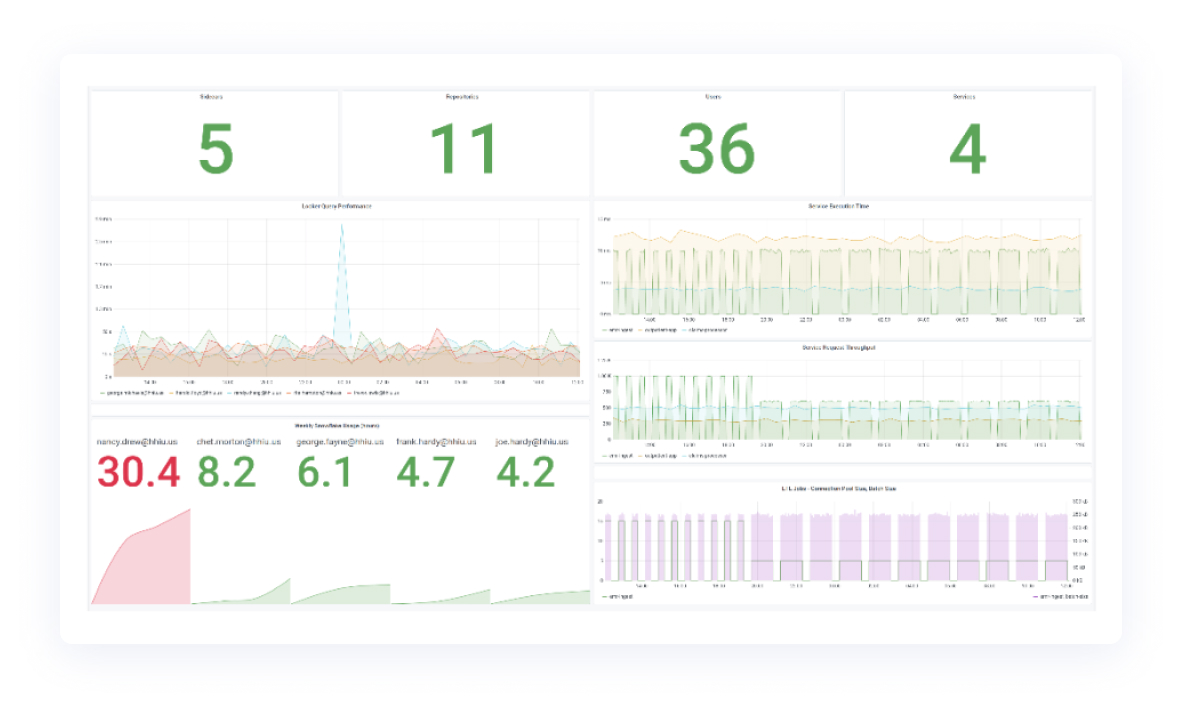

Use your existing dashboards for better visibility
Benefits
Immutable Activity Logs
Generate detailed, unified activity logs for all your structured and semi-structured data stores without impacting performance or scalability of the repositories. Send them encrypted to your favorite SIEM using signed API requests to protect against tampering. Build your dashboards in your favorite tools.
Metrics and Traces
Enhance your observability with enriched visibility into connections to your data repositories. Find out who ran that expensive analytics query from Looker, why the hourly ETL job is taking twice as long as normal, or who consumed the most Snowflake credits last week. Speed up your troubleshooting and RCAs.
Security Alerts
Did an application tenant perform a full table scan? Did someone change permissions on our database? Did a service use an unencrypted connection to log into my MongoDB? Cyral’s preconfigured rules alert you to undesirable behavior instantly. And you can always add more!
Integrations
Terminology
Terminology
SIEM
Security Information and Event Management systems enable the collection, transformation and analysis of data activity from various sources to help security teams detect threats, investigate events and pinpoint breaches.
APM
An Application Performance Management tool makes it easy to measure, monitor, and analyze key performance metrics of applications, microservices and infrastructure components so that traffic spikes, slow connections, queueing issues and caching problems are quickly identified and resolved.
Distributed Tracing
A distributed tracing framework makes it possible to trace the life of a request as it passes through a mesh of microservices until it is fully serviced. Tracing gathers timing and contextual data needed to troubleshoot latency, scalability and throughput problems in service mesh architectures.
Messaging / ChatOps
A workplace messaging platform allows teams within an organization to communicate with each other for collaboration as well as for approval based workflows for access to data, applications, infrastructure.
Incident Response
An Incident Response system helps an organization with the process of handling security events such as data breaches by streamlining and automating typical workflows and playbooks followed by security teams for alerting, diagnosis, forensics and remediation.
SOAR
A security orchestration, automation and response system helps security teams with incident data gathering, case management, and response workflow automation to quickly coordinate, respond and remediate security incidents.
ITSM
An IT services management tool helps IT teams in creating policies and processes for the management and support of IT services such as helpdesk, asset management and incident management.
Ready to Get Started?
Get started in minutes and explore how Cyral can protect your Data Mesh. You can also contact us to see a live demo.