Federated Authentication for Cloud Object Storage
Simplify Access Management for Cloud Data
Easily provision and manage access to cloud object storage using your existing identity provider. Simplify user administration by mapping identities to IAM roles. Eliminate tedious role and credential specification from access workflows.
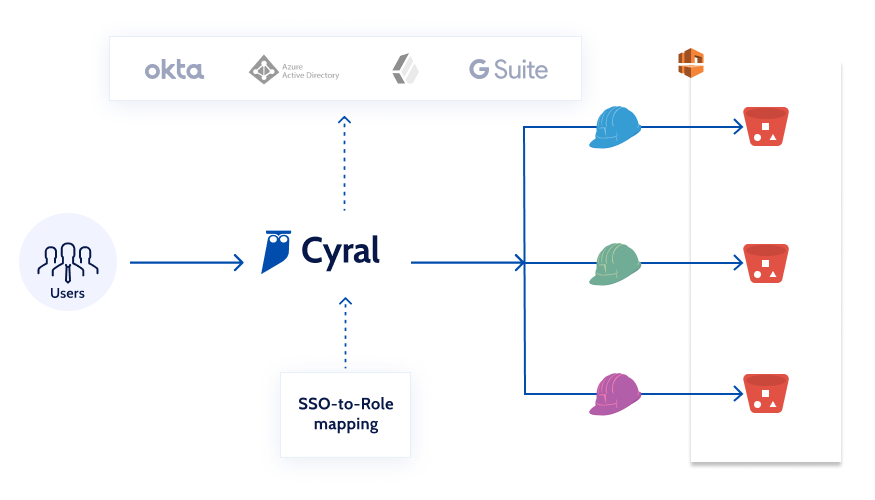
Managers Gain Simplified Access Controls
- Disentangle complex AWS policies by mapping your identity provider’s users and groups directly to AWS roles
- Eliminate manual user provisioning and de-provisioning
- Enable time-bound access grants for cloud object storage such as S3
Happier, More Agile Teams
- Access your cloud object storage using your existing IDP
- Eliminate role management from developer usage workflow
- Reduce scope of errors by simplifying access parameters
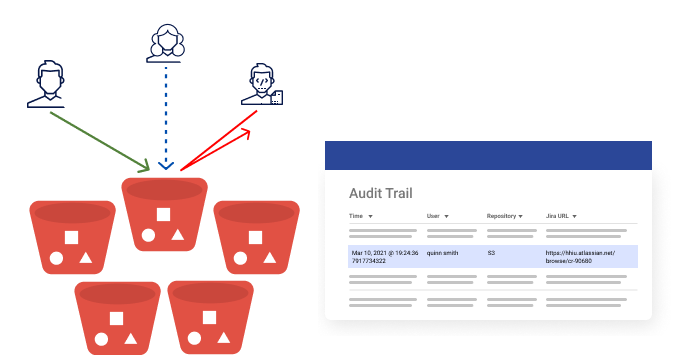
Empowered Security Teams
- Ensure least privilege and extend Zero Trust
- Raise alerts when you see anything that’s suspicious, and immediately block what’s disallowed
- Track every event in real-time and attribute each back to the identity that initiated it
Admin Setup Workflow

You Will Need
- Administrative access to your Cyral Control Plane
- Permissions to add a new application integration to your existing IdP
- Permissions to manage policies for the S3 buckets you’re protecting with Cyral
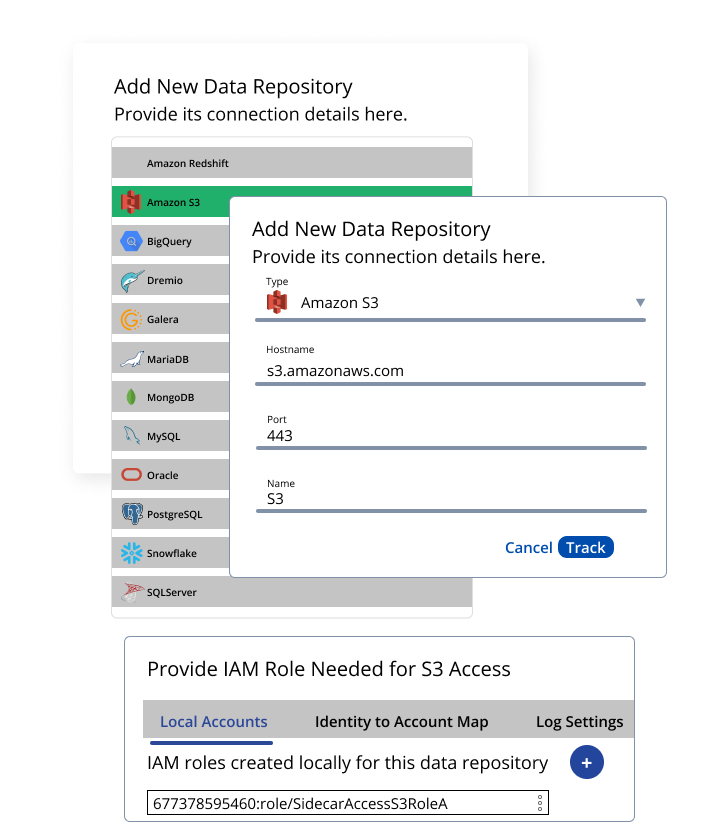
Configure Cyral
- Track the S3 repository with Cyral Control Plane
- Provide IAM role needed for accessing the S3 repo
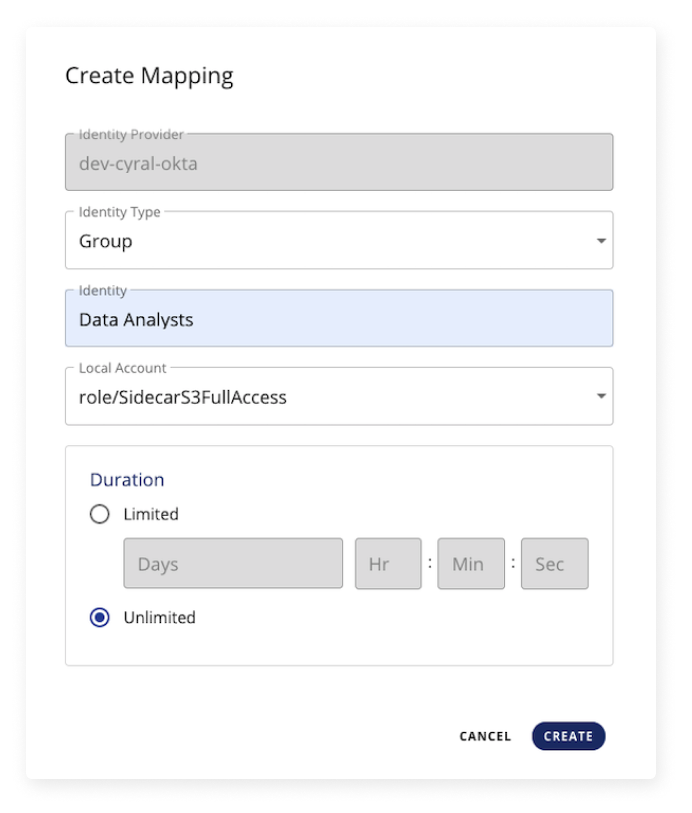
Set Up Identity Federation
- Map users or SSO groups in IdP to the IAM roles that can access S3
- Multiple such mappings may be created
- Put time-based expiration on the mapping
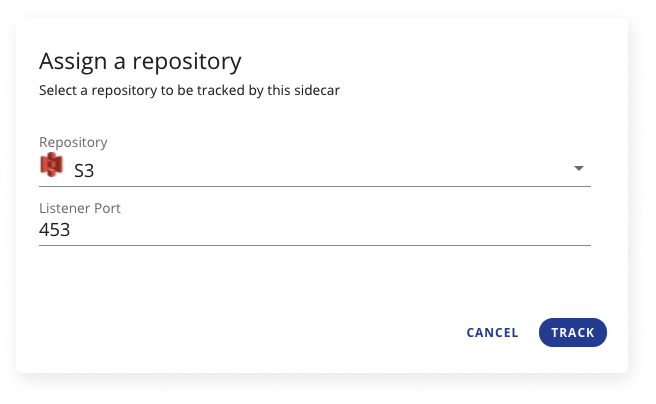
Redirect S3 to Cyral Sidecar
- Associate S3 repo with Cyral sidecar in your environment
- Ensure that the S3 bucket security policy restricts all access except the Cyral Sidecar (through assumed IAM roles, IP, or VPC)
Users Can Now Use S3 with IdP Tokens
- Log in using Cyral’s CLI tool or UI
Terminology
Terminology
IdP
An identity provider (IdP) authenticates a user and provides identity and access tokens for accessing other services. It uses SAML and OIDC protocols to interact with clients and is backed by a directory service storing user information.
Object Storage
Cloud object storage, also known as object storage or object-based storage, makes it possible to store, archive, back up, and manage high volumes of static or unstructured data—reliably, efficiently, and affordably. Unstructured data is data that cannot be organized easily into a traditional relational database with rows and columns. This data could include things like email, videos, photos, web pages, audio files, sensor data, and other types of media and web content.
IAM
Authentication and Authorization are two distinctly different processes in the field of Identity and Access Management (IAM).
There are numerous strategies utilized in modern computing systems, some of the oldest (not necessarily most secure) being PINs and Passwords. This is the “I” in Identity and Access Management (IAM).
The management and implementation of the policies that determine the authorization users are granted is the “AM” in IAM.
Get Started with a
Free Trial
Get started in minutes and explore how Cyral can protect your Data Mesh with our free trial. You can also contact us to see a live demo.

