Hello and welcome to TSD, your weekly blog post with top of mind security issues. TSD began as an internal newsletter that our Security Lead, Daniel Tobin, would circulate to the team each Tuesday. It proved to be a great resource for all of us so we thought, why not share it with all of you? Our hope is that it helps make you just a bit more secure.
Check back here every Tuesday for more TSD or sign up below to stay in the loop!
Please reach out to us directly, via security@cyral.com or on Twitter at @dant24 if you have any questions, concerns, tips or anything else!
- Security researcher and all around great person Dan Kaminsky passed away and SwiftOnSecurity has a great thread on how great a person he was. Read his own words for inspiration. My favorite memory was seeing him keynote BSidesSF in 2013 at DNA Lounge. RIP Dan.
- In the Codecov supply chain hack, Reuters is reporting that hundreds of customers were affected. Victim statements are starting to come in with HashiCorp and PasswordState the latest to announce. HashiCorp has taken precautions and has said their “investigation has not revealed evidence of unauthorized usage of the exposed GPG key”. ArsTechnica is reporting that 29,000 PasswordState users may have been affected. Supply chain attacks have gone from esoteric warning to competing at scale. Going after developers isn’t new especially if you think about Facebook and Apple being targeted in 2013 with watering hole attacks.
- Signal announced they found multiple issues with phone hacking software Cellebrite in a blog post. This is the latest salvo after Cellebrite that they announced support for Signal to their software. The issues found range from corrupting any and all reports to possible IP theft of Apple DLLs. In their Twitter announcement they put together a Hackers themed demo which is a must see. And the first fallout from this as a lawyer has asked for a new trial after this announcement according to Motherboard.
- Stanford undergrad student and former CISA advisor Jack Cable helped a number of people recover data from the QLocker ransomware after discovering a security flaw in the payment system. Cable was able to help out 50 people from around the world via CyberScoop
- Clubhouse had a bug where a user could become a ghost simply by logging in on 2 different phones. The bug was found by Katie Moussouris of Luta Security and the bug bounty was donated to @PayEquityNow.
- The University of Minnesota was completely banned from the contributing to the Linux kernel after researchers intentionally tried to submit insecure code multiple times. It was only after being caught many times that the drastic action was taken. Read more at ZDNet.
- And now, according to Yahoo News, a division of the US Post Office has “monitored significant activity regarding planned protests occurring internationally and domestically.” The Post Office? The bulletin was delivered to fusion centers which we first mentioned way back in TSD-14 in relation to the Blue Leaks.
Owl fun and facts:

It’s that time of year for owlets! If you’re in the San Francisco Bay Area, Great Horned Owls have returned yet again to Glen Canyon Park. If you can’t make it to the park, Mark Lipman of Open Studio Productions has been chronicling the escapades of the owl family. Read more about the owlets at The Chronicle.
A Shout Out:
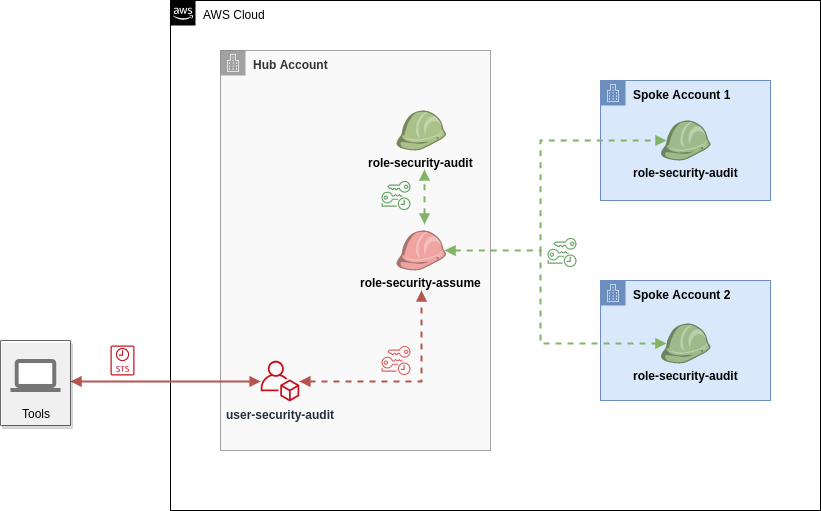
Marco Lancini from CloudSecList has released a brand new Security as Code Terraform module “which automates the setup of roles and users needed to perform a security audit of AWS accounts in a Hub and Spoke model.” You can read more about the concept of cross account auditing and then get started with the AWS Security Reviewer on GitHub.
That’s owl for now!


