Hello and welcome to TSD, your weekly blog post with top of mind security issues. TSD began as an internal newsletter that our Security Lead, Daniel Tobin, would circulate to the team each Tuesday. It proved to be a great resource for all of us so we thought, why not share it with all of you? Our hope is that it helps make you just a bit more secure.
Check back here every Tuesday for more TSD or sign up below to stay in the loop!
Please reach out to us directly, via security@cyral.com or on Twitter at @dant24 if you have any questions, concerns, tips or anything else!
- The Washington Post has a story about Premom, a fertility app that was collecting and selling extensive amounts of user data to ad firms without their consent. They also link to a Consumer Reports article digging into the privacy of period tracking apps. If you or anyone you know is using one of these, definitely review these articles so you’re aware of what you are sharing.
- TSD-18 featured the story about the great 2020 Twitter hack and now come more stories about the prevalence of vishing attacks, aka voice phishing. KrebsOnSecurity now has an in depth look at a phishing gang specifically offering these services for a host of other companies. KrebsOnSecurity then follows up the following day with a joint alert from the FBI and CISA. Be sure to check out the story as it includes a number of ways to protect against vishing.
- Sidenote: I was really vishing that they had a better name for it, but I do not hate it as much as “smishing”, aka SMS phishing…
- ZDNet is reporting on TeamTNT, a new botnet that does crypto-mining and is the first to also steal AWS credentials. The botnet scans for Docker systems without management APIs without a password as well as Kubernetes installations.
- Charlie Belmer, a security and privacy engineer at DuckDuckGo, wrote up his notes from Defcon on his blog Null Sweep. Talks include satellite eavesdropping, password cracking, scapy for DoS, GCP privileges and escalation and more.
- The Verge follows up with Tech Inquiry finding that ICE, everyone’s least favorite government agency at the beginning of the year signed a contract with everyone’s least favorite facial recognition company Clearview AI. As mentioned in TSD-13, Clearview may have ended their sales to private companies, but the government sales machine keeps rolling along.
- Meanwhile, Vice found that the California DMV had previously made $50 million selling data and now follows up with the revelation that there is a list of “nearly 98,000 entities that have had access to some form of DMV data”.
Owl fun and facts:
The above photo is a baby Spotted Eagle Owl photographed by Danelle Murray from the Owl Rescue Centre in South Africa. “Owl Rescue Centre, is based at Hartbeespoort in the North West Province, and now takes in more than a thousand owls every year through their rescue efforts. The owls are rehabilitated and when they can survive on their own in the wild, are released in the sanctuary – a farm which is located within a 12,000-hectare conservancy.” They just launched their store on Teespring where you can support the Owl Rescue Centre from the US. Checkout http://www.owlrescuecentre.org.za/ for more and follow Owl Rescue Centre on Twitter
A Shout Out:
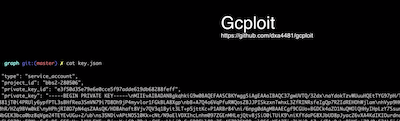
Allison and Dylan followed up their awesome talk from BSidesSF 2020 with even more info about GCP, service accounts and IAM roles at BlackHat / Defcon. Watch their full talk here without any of the overlays to be able to see the graphics better.
As part of their talk they have 2 repos out, GCPloit and an awesome set of security as code / policy as code examples for GCP using Hashicorp’s Sentinel product. Check those out here!
That’s owl for now!



