Hello and welcome to TSD, your regular blog post with top of mind security issues! TSD began as an internal newsletter that our Security Lead, Daniel Tobin, would circulate to the team each Tuesday. It proved to be a great resource for all of us so we thought, why not share it with all of you? Our hope is that it helps make you just a bit more secure.
Check back here every Tuesday for more TSD or sign up below to stay in the loop!
Hi Cyraloons and welcome to another week of TSD, your regular email / blog post with top of mind security issues, a few security tips for both work and home and at least 1 fun thing related to owls.
Please reach out to us directly, via security@cyral.com or on twitter at @dant24 if you have any questions, concerns, tips or anything else!
- Microsoft stepped up and bought the domain Corp.com during an auction to help prevent hundreds of thousands of Window’s computers sending sensitive information to whoever controlled it. KrebsOnSecurity originally reported on this in early in February. Microsoft and the former owner of Corp.com verified it’s sale this past Tuesday to KrebsOnSecurity
- KrebsOnSecurity has also been beating the drum about fraud during tax season due to limited controls. Given this, KrebsOnSecurity has reviewed the website for the Economic Impact Payment for Coronavirus Tax Relief and has found that it also has limited controls which could open it up to fraud including “for a large number of people who are disabled, poor or simply do not have easy access to a computer or the Internet”. More info at KrebsOnSecurity
- The Google Security and SRE teams have released their latest tome Building Secure and Reliable Systems. This book builds off the previous Google SRE books to “share best practices to help your organization design scalable and reliable systems that are fundamentally secure.” Read more and download it for free from Google’s Security Blog
- Scott Helme goes over how he secured his home network setup of Unifi hardware and offers 4 tips that can be used for any setup. Everyone if possible should use a good password, create a separate WiFi network, create a VLAN to isolate devices, and update all of your hardware. The hardware you use for this really eases this setup. Updating your hardware is super important if you’re running OpenWRT you should update sooner than later due to recently disclosed code execution vulnerabilities. More info at Ars Technica
Owl fun and facts:
Burrowing owls break pretty much all of the standard owl expectations. They are generally active during the day, live in open prairies, grasslands and other landscapes and will roost in previously used burrows such as those created by prairie dogs.

A Shout Out:
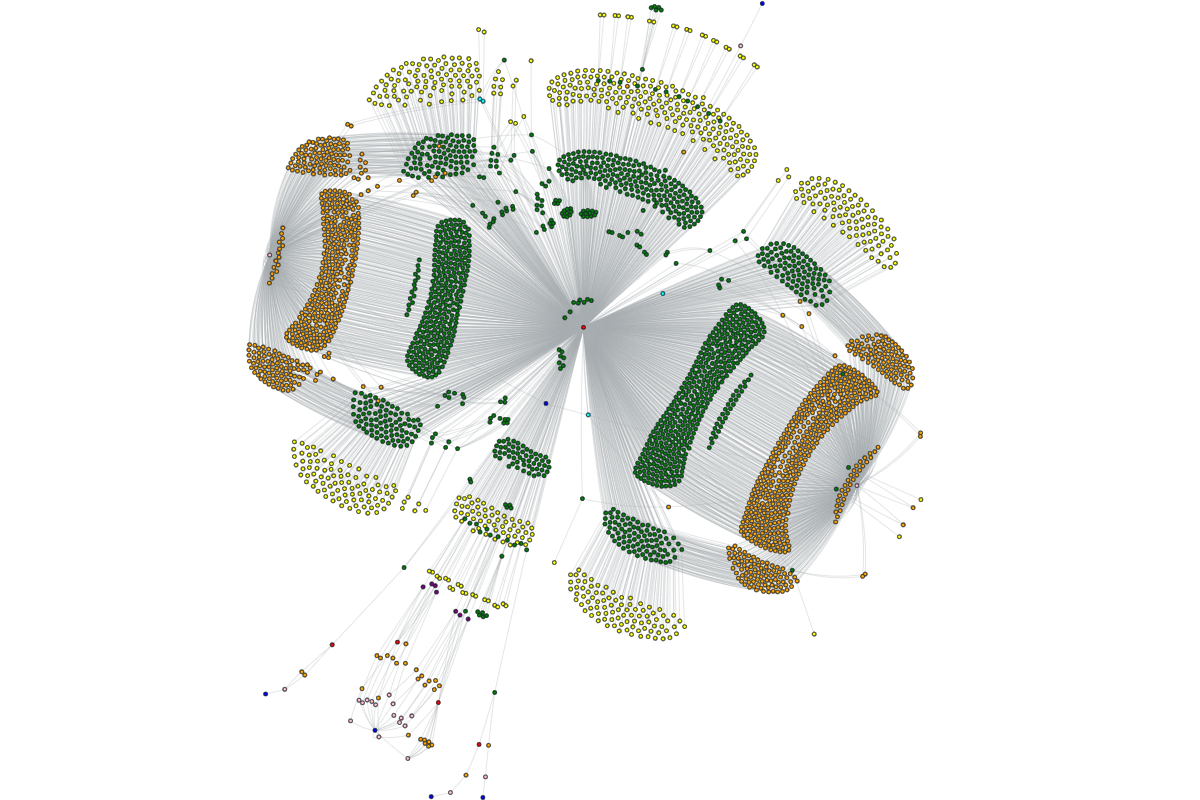
OWASP Amass is an open source project that gives you “In-depth DNS Enumeration, Attack Surface Mapping and External Asset Discovery!” What this means for you is that if you’re red team, blue team or purple team, you can use this to see exactly what is publicly exposed. Integrate this into your continuous security testing to alert when new applications come online that are not protected. An external asset inventory is a must so you can know what to protect! Download it and read the docs from the Amass GitHub today!
That’s owl for now!


