The Data Security community ubiquitously discovers new vulnerabilities. Staying vigilantly up to date with the latest exploits is crucial in order to protect your business, peers, and customers. In this security digest, we take a look at real life consequences of unauthorized use access and controls. We’ve curated news about Securitas’s unsecure AWS S3 buckets leading to a major breach, a record bug bounty involving webcam hijacking, Apple makes phishing attacks more difficult for attackers, exploits for local Windows vulnerability, and CISA adds eight new flaws to it’s exploited vulnerabilities catalog.
Faulty AWS Server Exposed 3TB in Airport Employee Records
An unsecured server has exposed sensitive data belonging to airport employees across Colombia and Peru. A misconfigured AWS bucket, which did not require any authentication to access, contained two main datasets related to Securitas and airport employees. Among the records were ID card photos, Personally identifiable information (PII), including names, photos, occupations, and national ID numbers. Read more at ZDNet.
Apple Pays $100.5K Bug Bounty for Mac Webcam Hack
A researcher who showed Apple how its webcams can be hijacked via a universal cross-site scripting bug (UXSS) Safari bug has been awarded what is reportedly a record $100,500 bug bounty. The bug could be used by an adversary as part of an attack to gain full access to every website ever visited by the victim. The bug-finder, Ryan Pickren, found that he could gain unauthorized camera access via a shared iCloud document that could also “hack every website you’ve ever visited.” Read more at ThreatPost.
Apple Makes 2FA Text Codes Safer from Phishing Attacks
According to MacWorld, Apple has implemented some modifications to the way the two-factor authentication (2FA) SMS autofill feature works on its devices. Whenever a user receives a two-factor authentication SMS on their iPhone, the feature shows the 2FA code above the on-screen keyboard, allowing for a 1-tap paste, to save time. However, phishing attackers have wised up to this feature (and other autofill technologies).
When users are directed to a phishing link by attackers and the website sends them a 2FA security code via SMS, the autofill option displayed for the code often serves to make the website appear legit when it is actually not. To prevent that from happening, Apple has introduced new layers of security to the feature, which now only offers to autofill a verification code if the domain of the website you’re on and the domain that sent the code match. Read more at National Cyber Security News Today.
Windows Vulnerability with New Public Exploits
A security researcher has publicly disclosed an exploit for a Windows local privilege elevation vulnerability that allows anyone to gain admin privileges in Windows 10. “Using this vulnerability, threat actors with limited access to a compromised device can easily elevate their privileges to help spread laterally within the network, create new administrative users, or perform privileged commands.” The vulnerability affects all supported support versions of Windows 10 before the January 2022 Patch Tuesday updates. Read more at Bleeping Computer.
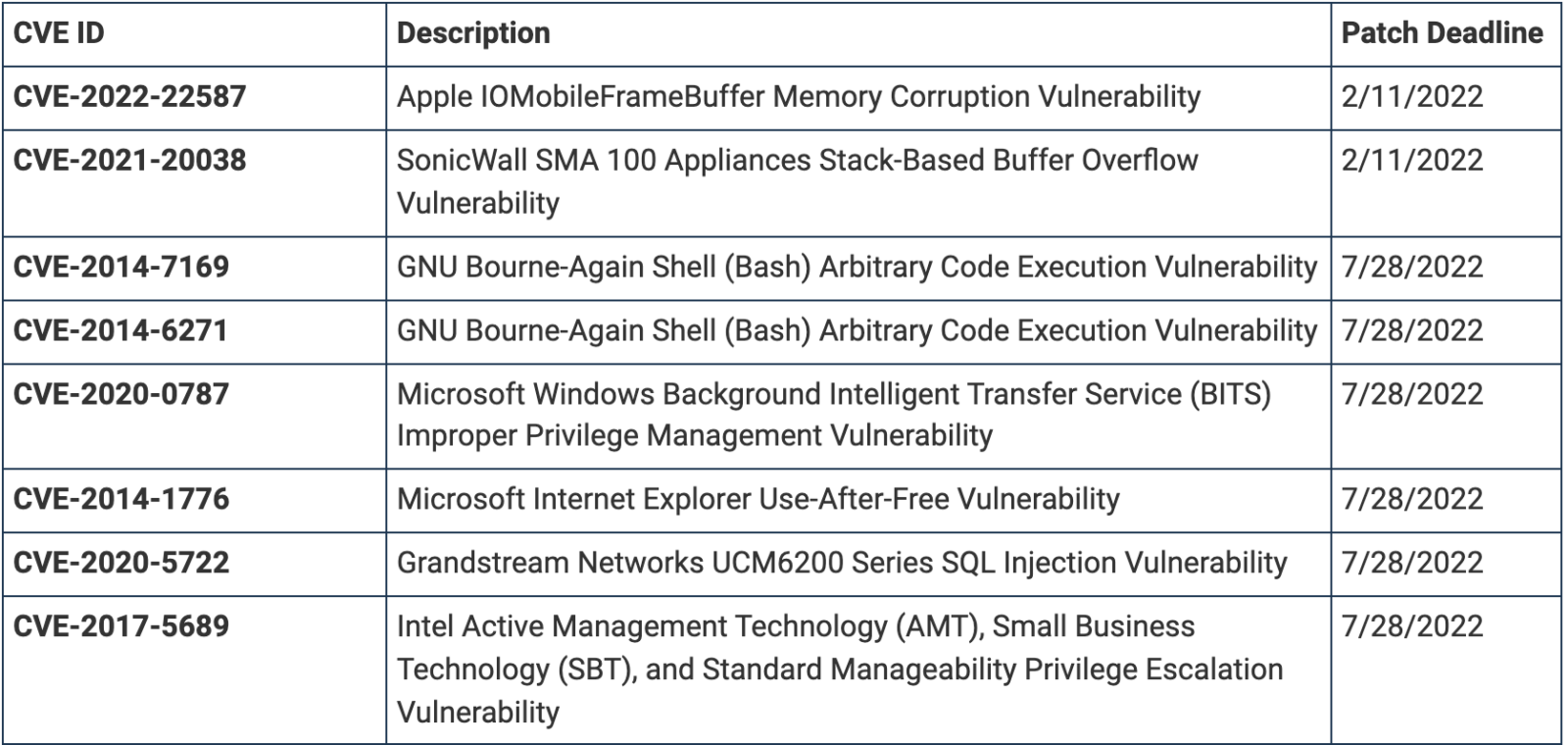
CISA adds 8 vulnerabilities to list of actively exploited bugs
The US Cybersecurity & Infrastructure Security Agency (CISA) has added eight more flaws to its catalog of exploited vulnerabilities that are known to be used in attacks, and they’re a mix of old and new. The goal of publishing these vulnerabilities is to raise awareness and remind federal organizations of their obligation to apply security updates by a specified strict deadline. Read more at Bleeping Computer.
Owl fun and facts:

CHICAGO — Snowy owls typically breed in arctic regions such as northern Canada and Alaska. But in the winter months, they can migrate as far south as Chicago’s lakeshore. And spotting one can be a magical experience, according to some in the birding community. Learn more.
About:
TSD began as an internal newsletter created by our security team that would be circulated to the team each Tuesday. It proved to be a great resource for all of us so we thought, why not share it with all of you? Our hope is that it helps make you just a bit more secure.
Check back here every week for more TSD or sign up below to stay in the loop!
Please reach out to us directly, via security@cyral.com or follow us on twitter @cyralinc if you have any questions, concerns, tips or anything else!