Delivering Zero Trust Architecture across your enterprise can be a daunting task. With so many capabilities to deploy across so many security controls, it’s no wonder that organizations often lose sight of their priorities. The good news is, if you start your journey with data in mind, you’ll be better off than many organizations. Why? Simply because the data is at the heart of the Zero Trust framework. At the end of the day, it’s your data that the attackers are after.
In this blog, we’ll take a look at some conventional practices in building a Zero Trust framework as it relates to data and speak about the most common mistakes organizations make. Then we’ll look at the data cloud and the security challenges it introduces. Finally, we’ll propose a slightly different approach to thinking about Zero Trust—and the one that we believe will simplify your journey to Zero Trust and get you to a better security posture sooner.
The Conventional Wisdom: You Can’t Protect What You Can’t See
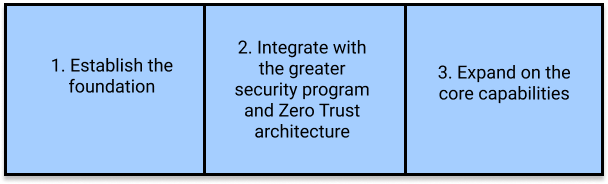
No matter what implementation sequence you follow, your steps will likely fall within this basic framework:
While there’s no debate around the basic premise of this sequence, what goes into each bucket is often debatable. The prevailing approach in the industry postulates, quite rightly, that it’s impossible to protect something that you aren’t aware of. In the world of data, which now lives across hundreds or thousands of repositories, be it databases, pipelines, or warehouses, this notion rings true with practitioners. Following this logic, the foundation that the organization chooses to build may start with discovery:
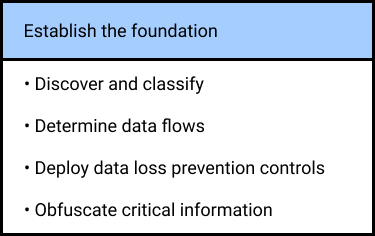
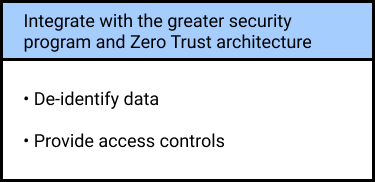
Only once this part of the journey is done (which can easily span months and even years), do organizations feel prepared to move on to the next step, where they integrate with the rest of their security program. Most often, their priority stack will look as follows:
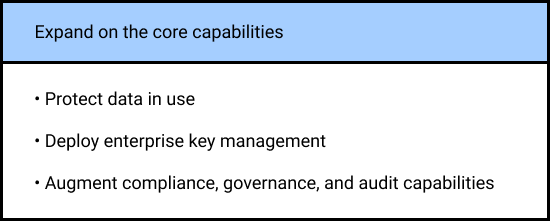
Eventually, these capabilities can be further expanded with a number of additional solutions to address the use cases that are more unique to the specific organization. For many security teams, the focus will be on at least a few additional areas, such as:
If the proposed sequence leaves you somewhat overwhelmed, you are not alone. While each of these capabilities undoubtedly adds value to the enterprise, in the world of limited time and resources, CISOs and CDOs have every right to wonder: is this the right order for me? Moreover, given the ever-changing nature of my data environment, are the priorities stacked in my favor in the long run? The answer to this question will certainly vary for each organization, but there’s a good chance that the path to Zero Trust can be shorter, and more importantly—more secure.
The Data Cloud Challenge
There’s every reason to take data security seriously. Aside from the fact that data will continue to be the main target of the attackers, it’s critical to keep in mind that we’re undergoing a once-in-a-generation shift in how we think about data. With more information moving from legacy on-premises databases to the cloud, and with more of it being distributed across tens, hundreds, and thousands of repositories, security practitioners are faced with new security challenges:
- Lack of identity: Unlike with application or infrastructure clouds, data cloud solutions do not offer the same uniform support for SAML/OIDC identity controls. In practice, this means that, despite the increasing heterogeneity of the data stores, a security team cannot rey on the same proven Identity and Access Management (IAM) solutions that have become a cornerstone of their security programs. Instead, they need to use separate credentials across data repositories, often defaulting to such risky practices as use of shared credentials and generous over-provisioning of privileges.
- Lack of visibility: Unlike application and infrastructure clouds, the data cloud consists of a much more diverse ecosystem of repositories, services, analytics tools, and services. Delivering the same uniform level of visibility and control across them is a known challenge that hasn’t been resolved. Added to that is a problem unique to databases specifically, whereby data access monitoring involves proxies or agents that slow down database performance. In reality, these native tools often end up disabled, leaving security teams driving blind.
- Lack of security: With no identity controls and no visibility, organizations face a challenge that didn’t exist in the on-prem world. At any given time, they cannot validate the real user or service responsible for a data access request. And without this information, they cannot determine if this user’s activity is benign, or if the user is exceeding their privileges. This, in a nutshell, is the exact opposite of a proper Zero Trust architecture.
Solving for Zero Trust in the Data Cloud
Considering these challenges, Cyral offers a different take on how to deliver Zero Trust to the data cloud. While the conceptual building blocks of this approach remain the same, the prioritization of what goes into each building block will be different. Let’s look at the proposed new sequence, and see how critical each step is.
Establish the foundation:
- Authenticate users and services (VERY CRITICAL): The biggest missing piece in the data cloud is identity. Given its fundamental role in Zero Trust, we recommend that organizations start by integrating their IAM capabilities with their data repositories. Cyral offers an intuitive, seamless way to integrate IAM into your data cloud and across all your data repositories.
- Deploy data loss prevention controls (VERY CRITICAL): When it comes to securing data, being able to observe any data request across any data repository is key. While in the past this required deploying proxies or agents, today you can use agent-less solutions that do not involve proxies. Cyral’s stateless interception technology is an example of how this can be done in practice with no impact on performance. Of note, with the first two capabilities in place, you should be able to generate rich logs that capture all data activity in a uniform way with full identity context.
- Provide access controls (VERY CRITICAL): With identity and observability in place, you can determine at a granular level who within your organization can access any specific piece of information. You can also create a centralized repository of policies that you can apply and enforce from a single place instead of managing them across a myriad of native policy tools.
Integrate with the greater security program:
- Connect with analytics and reporting tools (CRITICAL): Once you have logs to capture all data access events and enrich them with user context, you can make them a part of your security program by sending them to your SIEM, UEBA, reporting, and SOAR solutions. Reporting and auditing aside, one immediate benefit of this step is that you can immediately start to correlate data activity with other signals across your security infrastructure to catch lateral movement or any abnormal behavior. When done right, this would be the only step required to connect your data security with the rest of your Zero Trust architecture.
Expand the core capabilities (or not):
- Obfuscate and de-identify critical information (LIKELY CRITICAL): With identity information and full observability, you can—if you choose to—deliver a more granular way to produce data. For example, instead of prohibiting certain information from being accessed, you may determine that certain groups of users may see information partially. Any type of PCI, PII, or PHI information can fall under this category. While this capability is not critical, many industries will choose to prioritize it due to compliance or regulatory requirements, and this is why we believe that it will remain high on the priority list.
- Deploy enterprise key management (OPTIONAL): All security keys and tokens must be protected, but rolling out an enterprise key management solution may not be required in some industries or businesses. By using the native data obfuscation capabilities in your data security stack, you can minimize the amount of data that must be secured using encryption keys.
- Discover and classify data (OPTIONAL): Interestingly, data discovery and classification may not be as high on the list for most organizations. Data discovery and classification projects are notorious for taking a long time, but you will likely need to secure your top assets today. Our recommendation is to deliver Zero Trust where you need it now, and think of data discovery and classification as a long-term project that is aimed at identifying and covering gaps.
- Determine data flows (OPTIONAL): By the same token, determining data flows may be viewed as an optional long-term project, rather than an immediate security concern. As such, it may or may not be critical to a given organization. With proper observability controls in place, you will be able to see where your data comes from and goes to, and in many instances, this in itself will allow you to form a clear picture of data flows.
- Protect data in use (OPTIONAL): A stand-alone data protection solution may also be optional. Having the core ability to observe data access events and enforce granular controls should enable you to identify deviations from the baseline behavior without any added tools. With proper logging capabilities in place, your security analytics tech stack should be able to catch suspicious activity and alert or block unauthorized access. This can often be done using native controls, so there is a high chance that a dedicated data protection solution will not be required.
- Augment compliance, governance, and audit capabilities (OPTIONAL): The list of possible solutions and use cases in this category will likely vary drastically for every organization. As a rule, choosing an API-first, cloud-friendly data cloud security solution will provide a much more efficient and future-proof set-up. That said, considering their limited role in Zero Trust, we place these capabilities last, prioritizing robust data observability and logging controls as the key elements in the foundation for proper compliance and governance. (Learn more about database observability)
There is no doubt that each organization’s journey to Zero Trust is going to be different. As we have demonstrated, many of the capabilities that are commonly thought as foundational may in fact prove either non-critical, or not effective in delivering Zero Trust right here, right now. This is why we encourage organizations to think about their Zero Trust journey as a sequence of practices they will embrace, starting with those that add the most value to their security program. We believe that more and more organizations will choose identity and observability as the foundation for their Zero Trust architecture. As we’ve demonstrated above, there’s a good chance that by doing so, they will save themselves three or four extra steps along the way.


