Advanced Database Protection
Database Security Solutions:
Data Protection at the Database Level
Organizational data has never been more exposed. The number of data breaches in 2022 exceeded 1,800.
At the same time, cybersecurity spending hit record levels at over $150 billion.
Enterprises are spending more money, but their data is less secure. Not good.
Critical data is stored in a database. That’s what attackers are targeting — which means database security is the core of data security.
Ask yourself these questions:
1. What data do we have?
2. Where is the data stored?
3. Who has access to that data?
4. What are users doing with the data?
5. How do we manage access to the data?
6. What are our data security policies? How are they enforced?
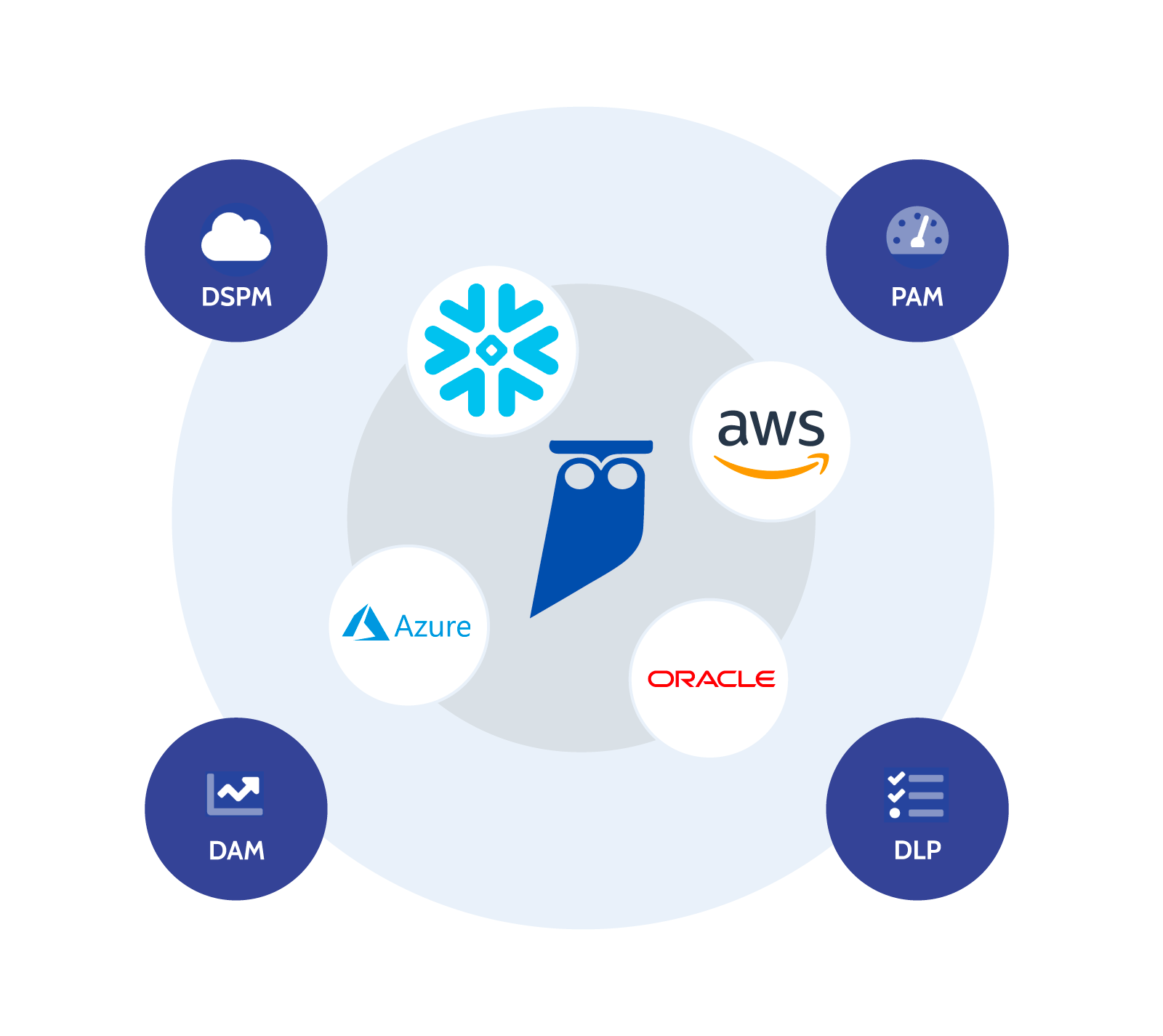
Cyral’s advanced database security solutions protect the data in your database by covering all six of these angles.
The problem? Enterprises are spending on peripheral projects and point solutions that don’t take this holistic approach:
Data Security Posture Management (DSPM)
helps discover, classify, and catalog sensitive data, but it does not enforce data security policies. Examples – Cyera, SymmetrySystems, Veza, Dasera
Privileged Access Management (PAM)
good for managing access control to infrastructure, and can be used to grant user access to databases, but doesn’t support application access to databases or field level access controls (e.g. data masking, filtering). Examples – StrongDM, Teleport
Data Loss Prevention (DLP)
provides enforcement but has no understanding of data inside the database, who should access the data or policies governing it. Examples – Symantec, McAfee
Database Activity Monitoring (DAM)
limited efficacy in cloud environments and no ability to monitor application users or enforce policies. Examples – Imperva, DataSunrise, IBM Guardium
Each of these projects should evolve into a comprehensive database security and governance approach within a similar budget and timeline. Fewer vendors means less integration and airtight security. Which means happy security teams, CISOs, and CFOs (and unhappy attackers) — just how we like it.
Don’t be one of the enterprises with a spend on a database security solution that falls short. Learn how to stop breaches at the target — the database — by downloading our database security guide “Why Data Security is Broken, And How to Fix It.”
